Scaling With Confidence: From Pilot to Platform Without Compromise
Explore security, compliance, and risk controls when transitioning pilots to scalable platforms, with practical steps that preserve speed while strengthening governance. We’ll connect architecture choices to audit outcomes, share cautionary tales from real migrations, and offer checklists you can adapt today. Ask questions, compare notes, and help shape approaches that keep engineers happy, customers protected, and regulators reassured.
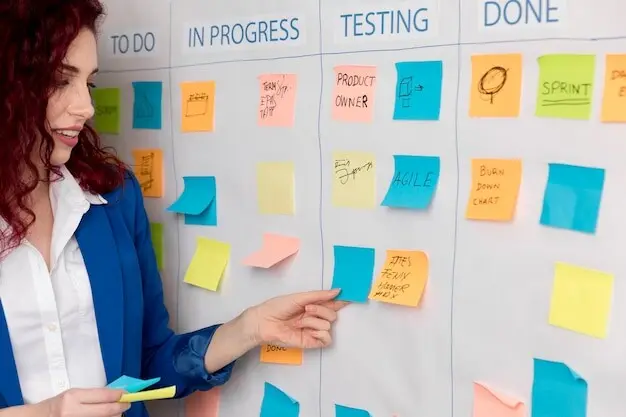
Governance by Design: Control Objectives That Guide Every Sprint
Shift control thinking from paperwork to product by expressing governance as clear, testable objectives. Map requirements to user stories, build acceptance tests for controls, and publish definitions of done. A short pilot at a healthcare startup proved this clarity reduced rework, friction, and audit surprises by orders of magnitude.

Identity, Access, and Secrets: Establish the First Trust Gates
Identity decisions compound fastest at scale. Centralize authentication, federate to your identity provider, and adopt zero trust defaults that assume breach. Implement SCIM for lifecycle, enforce strong MFA, and standardize workload identities with OIDC or SPIFFE/SPIRE. Rotate, vault, and attest everything without slowing deployments or onboarding.
Unify login across environments with SSO, strengthen sessions with phishing‑resistant MFA, and prefer short‑lived tokens over long‑lived keys. Scope access by job function, project, and environment. Document break‑glass paths with alerting so exceptional access is visible, accountable, and immediately rolled back when urgency subsides.
Provision least privilege automatically using roles generated from source truth, then grant time‑bounded elevation via approvals and chat‑ops. Apply the same pattern to CI/CD, support tools, and databases. Capture evidence automatically, demonstrating that powerful capabilities are constrained, audited, and promptly revoked when tasks complete or priorities change.
Codify environments with reproducible templates
Model environments as reusable modules with clear inputs, outputs, and ownership boundaries. Publish golden templates for common stacks. Require pull requests, automated tests, and security scans for every change. This consistency boosts reliability, speeds approvals, and makes evidence collection repeatable instead of painful, rushed, and error‑prone.
Prevent misconfigurations with policy as code
Enforce preventative controls through organization policies, service control policies, and admission controllers. Express intentions in code, version them, and test like applications. Fail fast and loudly when violations occur, providing actionable messages developers can fix within minutes rather than discovering issues days later during audits.
Detect and fix drift before it becomes debt
Continuously compare desired state to reality, detect unauthorized changes, and remediate automatically. Use drift reports to focus coaching and tune guardrails. Integrate alerts with on‑call rotations so ownership is clear, response is swift, and lingering configuration entropy never snowballs into outages, excessive costs, or compliance gaps.
Data Protection and Resilience Across Growth Stages
Protect data across its lifecycle with encryption, tokenization, masking, and minimization. Choose key hierarchies and rotation cadences aligned to risk. Honor residency and retention rules by design. Regularly test restores and failovers so customer trust is backed by verifiable resilience rather than hopeful assumptions or outdated runbooks.
Observability, Detection, and Incident Preparedness
Visibility enables trust. Capture logs, metrics, and traces where decisions are made. Normalize events into your SIEM, prioritize detections by impact, and bind runbooks to alerts. Practice incident response through tabletop exercises so communications, forensics, and containment are familiar routines rather than chaotic improvisation under pressure.

Instrument signals that matter to safety and trust
Decide which signals directly protect customers, revenue, and reputation, then instrument those first. Retain logs at lengths matching regulatory and investigative needs. Ensure searchability and integrity. Build dashboards that combine reliability SLOs with security indicators, helping engineers spot anomalies early and discuss risk using shared, actionable context.
Operationalize detection with prioritized playbooks
Turn noisy alerts into prioritized playbooks with clear triggers, owners, and success criteria. Escalate by impact, not guesswork. Automate common responses through SOAR. Track mean time to detect and contain, converting lessons from every incident into backlog items teams actually complete before the next surprise arrives.
Practice incident response until it feels routine
Schedule recurring drills, rotate roles, and practice cross‑team coordination, including legal and communications. Timeboxed exercises expose gaps in access, tooling, and decision authority. Capture improvements, assign owners, and follow through. The goal is muscle memory that reduces panic and protects customers even on difficult weekends and holidays.
Turn standards into developer stories and tests
Convert abstract clauses into concrete user stories, pull requests, and tests so developers see purpose and boundaries. Provide examples and scaffolded templates. Tie stories to business outcomes like faster onboarding or safer releases. When people understand why, conformance rises naturally and corrective conversations become collaborative rather than adversarial.
Automate evidence and continuous control monitoring
Instrument controls to emit verifiable events, capture artifacts in a tamper‑evident store, and maintain dashboards showing coverage and health. Replace audit scrambles with continuous readiness. Invite stakeholders to review progress routinely, catching gaps early while demonstrating diligence to customers, partners, and regulators without derailing delivery schedules.
Risk Management in Motion
Make risk a living conversation. Maintain a transparent register, quantify impact ranges, and watch leading indicators, not just lagging metrics. Revisit assumptions after incidents, new integrations, or regulatory changes. Document decisions with owners and review dates so choices adapt as information improves and context evolves.

All Rights Reserved.